Our product lines
Innovation to protect your information when most at risk.
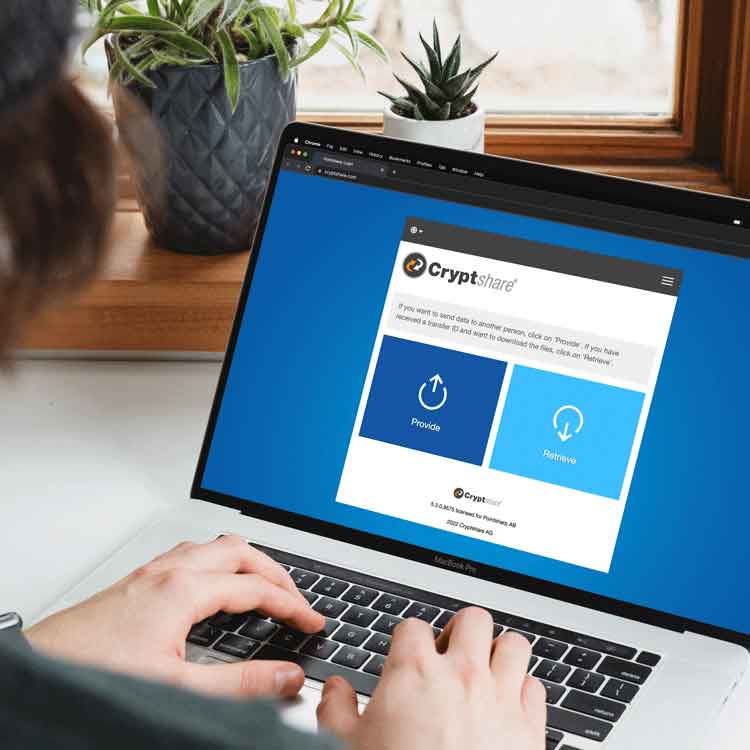
Cryptshare Web App
Users and their external communication partners can use Cryptshare via browser.
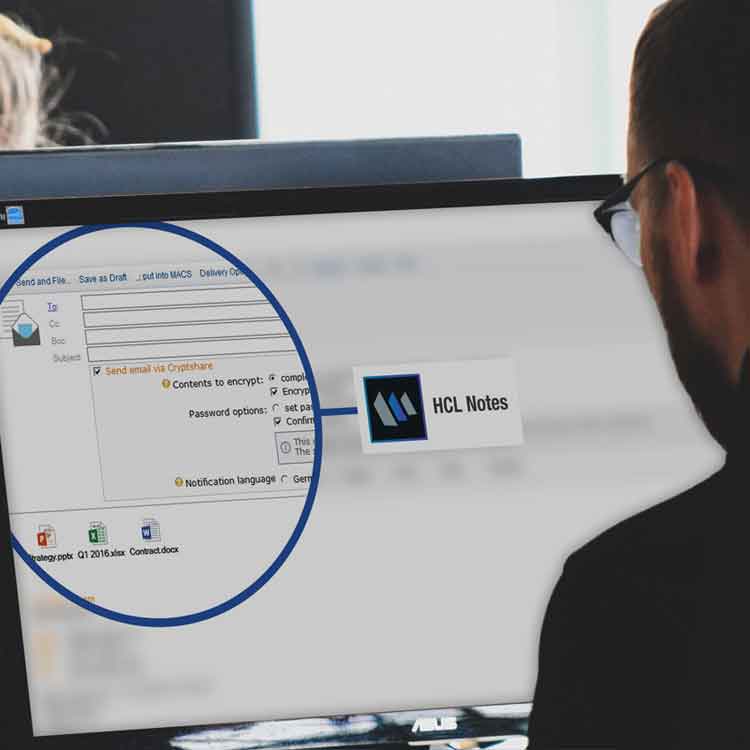
Cryptshare for Notes
The HCL Notes integration makes all features available in your Notes.

Customer Story
RECARO Group - Customer since 2017
"Cryptshare convinced us due to its straightforward administration and its easy to use Outlook add in."