Ransomware Protection
Why ransomware is so dangerous and how you can protect yourself against it.
What is Ransomware?
Ransomware, or crypto trojans, encryption trojans, blackmail trojans or extortion software, are malicious programs developed to allow intruders access to a computer's data. Access to the computer's data is either blocked, or all data is encrypted and only unlocked again against payment of a ransom. In this country, the best-known bogeymen are probably Locky, the BKA Trojan, WannaCry and Emotet.
"Ransomware is not just malicious code that destroys files; a complete criminal value chain has been created."
Matthias Kess, CTO Pointsharp GmbH
How does a ransomware infection work?
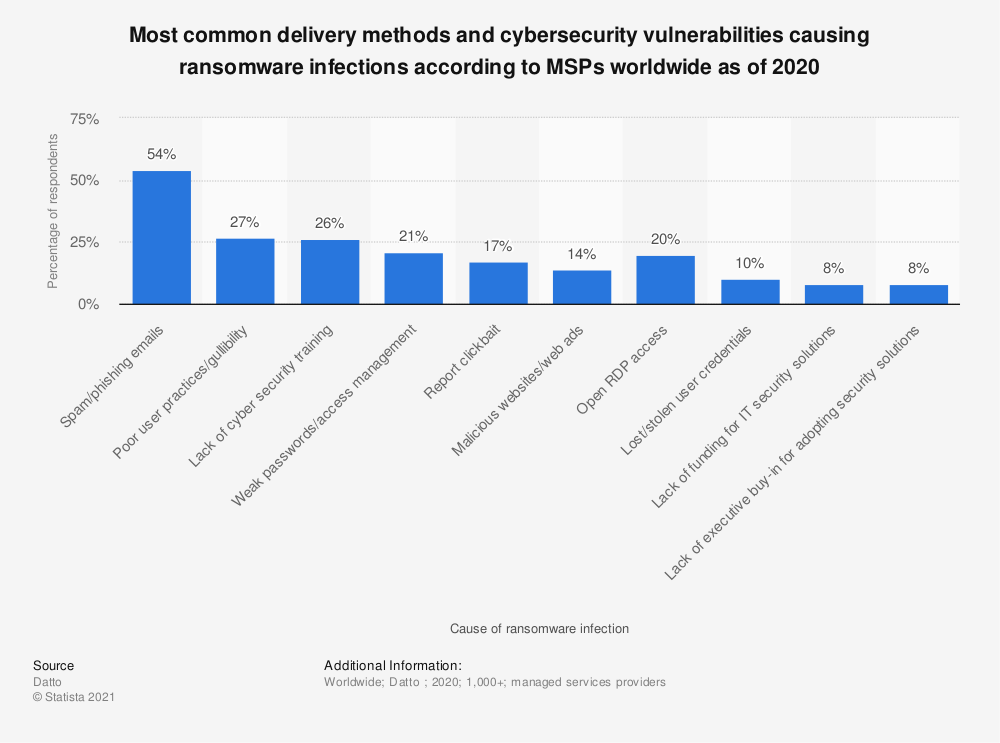
Email is the most common gateway for ransomware
Phase 1: Infection
How does ransomware enter a company?
Ransomware can enter via file types where it is possible to deposit active code. For example, in Office macros or embedded in PDF files. These files are often sent as email attachments. However, it is also possible to become infected by visiting an infected website, i.e. you can also catch Emotet by clicking on a link.
The programmers of the malicious codes often exploit vulnerabilities in operating systems, browsers or email clients that the software manufacturers themselves are not yet aware of or at least have not yet closed (so-called zero-day gaps).
Phase 2: Embedding
At first, ransomware does not make itself noticeable and nests on the computer. If, for example, Emotet infects a computer which Outlook is installed on, it intercepts the communication. It notes with whom and on what topics emails are exchanged. It then generates an email from one's own mailbox with a text and a topic about which one has already exchanged with known recipients. For the recipient, this looks like a legitimate email from the sender's hand.
Email is therefore the riskiest gateway for ransomware.
Phase 3: Dissemination and collection of data
Emotet tries to spread horizontally to other computers. To do this, it uses brute force attacks with known passwords. Of course, it is particularly helpful for Emotet if a computer or user with administrative rights can be infected. With administrative rights, it then spreads horizontally to as many machines as possible and keeps contact with the attackers' command and control centre. On the machines it has infected, as much account data, passwords (especially of administrative accounts) and personal data as possible are collected and sent to the attackers.
Phase 4: Blocking and Extortion
The attackers gather information and then wait for the appropriate moment to attack the company.
For example, at the weekend they can
- delete all back-ups
- encrypt machines
- and then leave a message with their demands.
A ransomware infection can therefore be present for months before anyone notices it. That's why it's very difficult to track where the ransomware came from and how it spreads.
Phase 5: Negotiation, payment and release of data
The instant messaging service Telegram is often used to negotiate the ransom, as the secure architecture of this service makes tracing difficult. Some ransomware has already integrated a corresponding negotiation functionality. Provided you agree on a sum with the extortionists, the ransom is usually paid in the form of bitcoins.
However, experts and investigating authorities often advise against accepting a ransom demand; too often, the data is not decrypted despite payment and the computers are still locked.

How can you protect yourself from ransomware?
Can ransomware be prevented?
Ransomware cannot be prevented, but there are various methods to protect against it and to react to it.
Tips for protection against ransomware
To protect yourself from ransomware, you can try to close as many gateways as possible.
no longer accept any files at all via email that could contain malicious code.
prevent or limit the execution of any code for file types that could be affected.
stop receiving and sending any files that contain executable code.
company-wide blocking of USB ports on computers and prohibition of USB sticks.
It is also very important that employees are informed that they should be cautious when files want to execute macros. If in doubt, consult the author of the file. The same applies when clicking on links.
Adapt back-up strategy
A possible reaction to Emotet is, for example, back-up software that detects when a lot of files on the computer are changed. This software then locks the computer and offers to restore the back-up. However, it can happen that the "sleeping" ransomware is already saved in the back-up, infected files are restored and the attack is triggered again after some time. Only back-ups that are offline and, if possible, go back a long time (several months) are helpful here.
How can ransomware be prevented with Cryptshare?
Alternative transfer path
Cryptshare uses a way to transfer files and messages that ransomware cannot automatically attack at the moment. Since attackers want to make money with as little effort as possible, you become rather uninteresting as an extortion victim.
Password protection
To protect against ransomware, the option "send without password" should also be deactivated. This is because if a password exchange is required between sender and recipient, there is a chance that the sender is not genuine.
Logging all processes
With Cryptshare much more information is logged, because the Cryptshare server logs who sent something and when. Therefore, the attacker loses their anonymity to a certain extent and takes a greater risk with regard to tracing.
Every hurdle reduces the probability of being blackmailed by ransomware
It's like protecting houses against burglary: The harder you make it for the attackers, the less likely they are to go that route. Ultimately, there are any number of targets, so the attackers naturally choose the ones that are as lucrative as possible and at the same time as easy as possible to conquer.
Therefore, there is not THE one system to prevent ransomware, you can only take different protective measures. Cryptshare is one of many possible protective measures and a good way to make electronic communication more secure.